STO Smart Contracts
A Platform to Create STO Smart Contracts
As one of the most expansive firms for all your technology and ERP needs, Prolitus provides its users with all the necessary STO (short for Security Token offering) services. One crucial aspect of STO is building a platform to support STO smart contracts, and yes, we, at Prolitus, strive to offer the best STO smart contracts development services along with properly conducted audits for the same.
Custom smart contract capabilities provided by Ethereum paves way for new ideas that can be applied in a distributed, trusty, and immutable way. Ill-designed smart contracts, on the other hand, are prone to theft and may lead to huge financial losses and thus need to be meticulously tested by experts. Team of full-stack Blockchain experts at Prolitus have the acumen to design, develop, and test feature-rich STO smart contracts as per the specific requirement of their clients. With a robust STO smart contract platform in place, developers can enjoy better security along with reduced overhead cost and complexity.
But, as suggested above, not only we offer smart contract services but also the most legitimate smart contracts audit service ensuring the contracts stay free of any errors or flaws. After all, smart contracts are easily susceptible to various flaws related to security along with software vulnerabilities. Therefore, we prepare an expansive audit report detailing various inputs from the data by testing the external code for any errors thanks to our trusty security model. Further, we also implement codes to all the paths we can possibly touch so as to evaluate different states that can be achieved.
Token Creation:
We set up fully compatible ERC-20 compliant tokens,which besides having the main functions can be used as a base for developing more sophisticated applications rather than just transferring them.
Token Issuance:
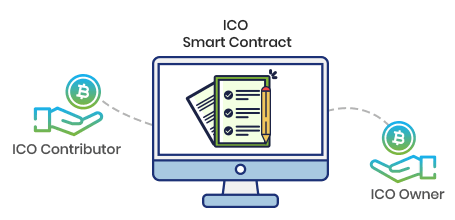
We help in managing issuance of smart contracts during private sales and ICO’s. The contract helps in automatically transferring tokens as soon as the payment is credited.
Escrow Contract:
It helps to write contracts that allows storage of ether and ERC-20 tokens and issuance of ether slash token, based on pre-defined business rules.
Custom Smart Contract:
We design custom smart contract based on requirement related to issuance of token, funds collected, distribution of funds to various partners/ investors.
Smart Contract Audit:
Smart contracts are susceptible to security flaws and vulnerabilities. Such faults and errors have costed the cryptocurrency ecosystem with billions of dollars. At Prolitus, we provide standardized smart contract audit services by verifying your smart contract against our library of already identified issues. We further validate your contract by ensuring that it is performing as designed to and is free of any functional and security vulnerabilities. We also help you optimize your smart contract through gas analysis thereby preventing users from spending unnecessary fees on Ethereum transaction. Ultimately, a detailed audit report regarding every function of your contract and its’ performance is provided.
Process Flow:
At Prolitus, we ensure that your smart contract works as designed to. Our experts carefully read through your smart contract codebase to identify the presence of discrepancies and vulnerabilities. They then share a detailed report of the issues identified besides providing suggestions about ways to fix them.

Smart Contracts AUDIT SERVICE
Taint Analysis
Smart contracts are audited for parts where the chances of external code running improperly is high.
Data Validation
Input data that is used to demand functions are tested to ensure that smart contracts are safe from attack vectors.
Model Checking
Smart contracts are tested by a security model to observe whether they perform according to intended functionality.
Control Flow Analysis
Code implementation is charted out to all possible paths to evaluate different states that can be achieved.
Fall Back Mechanisms
To do away with probable worst case scenarios, smart contracts are work-shopped along with development teams with associated fall back mechanisms.
Audit report
A detailed audit report is compiled basis the intensity of the audit conducted. Besides key findings, the report also enlists the security fixes undertaken by the project team.
To learn more about Prolitus STO Smart Contract development & Audit service, contact us at [email protected]


